Wireshark是世界上最重要的网络协议分析器,并且是许多行业和教育机构的事实上的标准。
广告
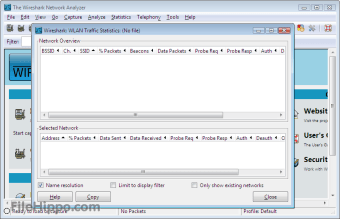
- 深入检查数百种协议,一直在增加
- 实时捕获和离线分析
- 标准三窗格数据包浏览器
- 多平台:在Windows,Linux,OS X,Solaris,FreeBSD,NetBSD和许多其他操作系统上运行
- 捕获的网络数据可以通过GUI或TTY模式的TShark实用程序进行浏览
- 业界最强大的显示过滤器
- 丰富的VoIP分析
- 读/写许多不同的捕获文件格式
- 使用gzip压缩的捕获文件可以即时解压缩
- 可以从以太网,IEEE 802.11,PPP / HDLC,ATM,蓝牙,USB,令牌环,帧中继,FDDI等读取实时数据(取决于平台)
- 对许多协议的解密支持,包括IPsec,ISAKMP,Kerberos,SNMPv3,SSL / TLS,WEP和WPA / WPA2
- 可以将着色规则应用于数据包列表,以进行快速,直观的分析
- 输出可以导出为XML,PostScript®,CSV或纯文本