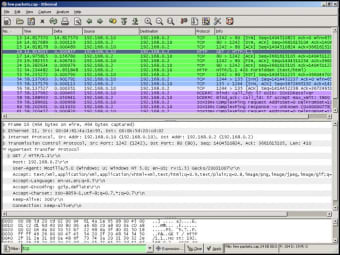
Wireshark jest wiodącym na świecie analizatorem protokołów sieciowych i jest de facto standardem w wielu branżach i instytucjach edukacyjnych.
Reklama
- Dogłębna kontrola setek protokołów, z ciągłym dodawaniem kolejnych
- Przechwytywanie na żywo i analiza offline
- Standardowa przeglądarka pakietów z trzema oknami
- Wiele platform: działa w systemach Windows, Linux, OS X, Solaris, FreeBSD, NetBSD i wielu innych
- Przechwycone dane sieciowe można przeglądać za pomocą GUI lub narzędzia TShark w trybie TTY
- Najmocniejsze filtry ekranowe w branży
- Bogata analiza VoIP
- Odczyt / zapis wielu różnych formatów plików przechwytywania
- Pliki przechwytywania skompresowane za pomocą gzip można rozpakować w locie
- Dane na żywo mogą być odczytywane z sieci Ethernet, IEEE 802.11, PPP / HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI i innych (w zależności od platformy)
- Obsługa odszyfrowywania wielu protokołów, w tym IPsec, ISAKMP, Kerberos, SNMPv3, SSL / TLS, WEP i WPA / WPA2
- Reguły kolorowania można zastosować do listy pakietów w celu szybkiej i intuicyjnej analizy
- Dane wyjściowe można eksportować do formatu XML, PostScript®, CSV lub zwykłego tekstu