Wireshark è il principale analizzatore di protocollo di rete al mondo ed è lo standard de facto in molti settori e istituzioni educative.
- Ispezione approfondita di centinaia di protocolli, con l'aggiunta di altri in continuazione
- Acquisizione in diretta e analisi offline
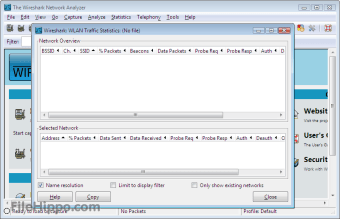
- Browser a pacchetti standard a tre pannelli
- Multipiattaforma: Funziona su Windows, Linux, OS X, Solaris, FreeBSD, NetBSD, e molti altri
- I dati di rete catturati possono essere sfogliati tramite una GUI, o tramite l'utility TShark in modalità TTY-mode
- I filtri di visualizzazione più potenti del settore
- Ricca analisi VoIP
- Lettura/scrittura di molti diversi formati di file di acquisizione
- I file di cattura compressi con gzip possono essere decompressi al volo
- I dati in tempo reale possono essere letti da Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI e altri (a seconda della vostra piattaforma)
- Supporto di decodifica per molti protocolli, tra cui IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP e WPA/WPA2
- Le regole di colorazione possono essere applicate alla lista dei pacchetti per un'analisi rapida e intuitiva
- L'output può essere esportato in XML, PostScript®, CSV o testo in chiaro